Key Takeaways
- Cybersecurity lead generation requires trust-first outreach — security buyers are professionally trained to distrust vendors, making generic B2B playbooks completely ineffective.
- Only 5–15% of B2B prospects are in an active buying cycle at any given time — intent signals help you find that minority instead of blasting your entire TAM.
- Buying committees in cybersecurity typically involve 6–10 stakeholders, including CISOs, SOC leads, GRC, IT, and procurement — single-threaded outreach misses most of the deal.
- Compliance deadlines (CMMC, HIPAA, SOC 2, GDPR) create time-bound urgency and budget mandates that outperform generic security pitches as outreach triggers.
- Responding to inbound leads within 5 minutes makes you 21x more likely to qualify them — yet the average B2B vendor takes 47 hours to follow up.
- The cybersecurity companies winning pipeline in 2026 are investing in relevance and precision over reach and volume.
Most cybersecurity vendors have a pipeline problem — and it's not the product's fault.
The real issue is that B2B lead generation for cybersecurity companies doesn't follow the same rules as the rest of B2B. Security buyers are skeptical by profession. They scrutinize every vendor claim, distrust unsolicited outreach, and self-educate extensively before speaking to any sales rep.
Generic messaging doesn't just underperform — it actively signals that you don't understand their world.
The market itself is enormous. According to Gartner, worldwide security and risk management spending will reach approximately $213 billion in 2025 and climb to around $240 billion in 2026, driven by AI/ML security, cloud posture management, and managed services.
With that kind of budget flowing, competition for the same security conversations has never been more intense.
This guide breaks down 10 proven cybersecurity lead generation strategies — built around how security buyers actually research, evaluate, and make decisions.
Whether you're running a cybersecurity startup or scaling an established vendor, these are the plays that actually produce qualified pipeline.

Why Cybersecurity Lead Generation Is Different from Regular B2B
The standard B2B outbound playbook — broad list, generic email sequence, high volume — fails hard in cybersecurity. Here's why B2B lead generation for cybersecurity companies requires a completely different approach.
Security Buyers Are Trained to Distrust You
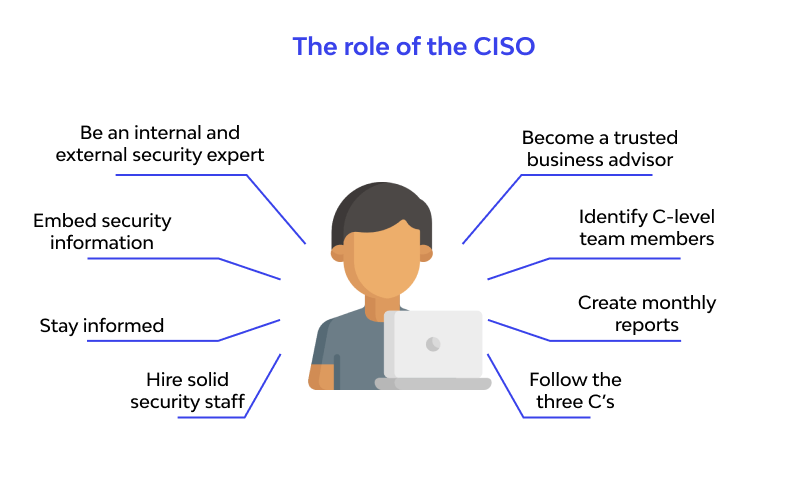
CISOs, SOC leads, and IT Directors deal with social engineering, phishing, and manipulative vendor tactics as part of their daily job. Anything that reads as generic, overhyped, or low-effort gets ignored — or worse, flagged internally as suspicious.
Your outreach is competing not just with other vendors, but with your buyer's professional instincts. That means credibility signals, peer validation, and relevance aren't nice-to-haves. They're the price of entry.
Buying Decisions Involve Multiple Stakeholders
Cybersecurity buying committees typically involve 6–10 stakeholders — spanning CISOs, SOC leadership, IT infrastructure, identity and access management (IAM), GRC teams, and procurement. Reaching only one person means most of the deal is happening without you.
Single-threaded outreach is one of the top reasons cybersecurity vendors stall in the pipeline even after a strong first meeting.
Trust Is Built Before the First Conversation
According to Forrester, 92% of B2B buyers begin their research already thinking about at least one specific vendor — and 41% favor a vendor before formal evaluation even begins. In cybersecurity, that shortlist is built through thought leadership, peer networks, community presence, and review platforms — long before any SDR sends a connection request.
The winning formula isn't more volume. It's intent signals + technical credibility + precision outreach. Everything below is built on that foundation.
Top 10 Lead Generation Secrets for Cybersecurity Companies
1. Target Intent Signals, Not Just Job Titles
Most cybersecurity lead generation programs start with job title filters and a static list. That's a fast way to burn through the budget on prospects who aren't in any buying mode.
The sharper approach is layering intent signals on top of ICP targeting. What does an in-market cybersecurity buyer actually look like in the wild? A company in their industry just had a public breach. Their CISO LinkedIn activity shows engagement with compliance content. They're actively posting reviews on Gartner Peer Insights. They've been running job postings for a security operations role for 60+ days.
Layer multiple signals together — and you've identified a company in urgent buying mode before anyone else has reached out. Tools like Bombora, LinkedIn Sales Navigator job change alerts, and competitor review activity on G2 all surface these signals when set up correctly.

2. Use Compliance Deadlines as a Lead Generation Trigger
Compliance-framed outreach is one of the highest-performing angles in B2B lead generation for cybersecurity — because it targets buyers with a real budget mandate and a hard deadline. That combination produces urgency that generic security pitches never generate.
Key compliance windows in 2026 to build outreach around:
- CMMC Level 2 readiness for defense contractors and supply chain vendors.
- HIPAA updates and audit cycles for healthcare and adjacent industries.
- SOC 2 Type II renewal windows for SaaS companies handling sensitive data.
- GDPR/NIS2 enforcement for companies with EU operations.
- ISO 27001 certification preparation for enterprise procurement requirements.
The messaging angle that works: "You have a [specific deadline] — here's where most companies in your industry have gaps." Specific. Deadline-anchored. Backed by evidence. That's what gets a CISO to respond.
3. LinkedIn Outreach to Security Decision-Makers
LinkedIn is the highest-trust outbound channel for reaching CISOs, VP of Security, and IT Directors — and for cybersecurity vendors specifically, it's the primary channel where security leaders are already engaged professionally.
The key is targeting precision. Sales Navigator lets you filter by job function, seniority, company size, industry, and technologies used. For cybersecurity, you can layer in signals like CISO hiring activity, recent company funding, or technology stack indicators that suggest a buyer is actively evaluating or modernizing their security infrastructure.
Messaging approach matters as much as targeting. Lead with a specific risk framing tied to their industry or company context — not product features. A LinkedIn connection request that opens with a relevant insight about a recent breach pattern in their vertical will outperform a standard "I'd love to connect" message every single time.
4. Build Credibility Through Thought Leadership Content
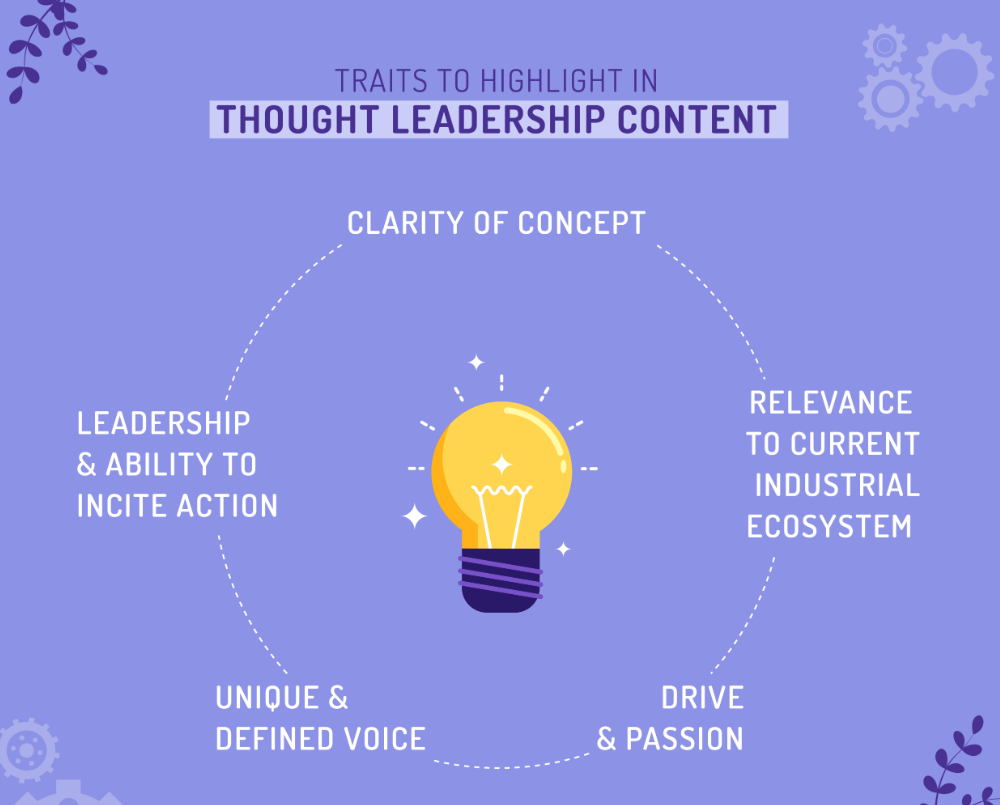
Cybersecurity buyers self-educate before talking to any vendor. Your content isn't a marketing asset — it's your first sales rep. And if it's generic, your credibility takes a hit before the conversation even starts.
The content formats that actually build trust with security buyers:
- Original threat research and breach pattern analysis tied to specific industries.
- Compliance guides with actionable gap assessments (not just explainers).
- Technical whitepapers with enough depth to signal real expertise.
- Breach post-mortems that walk through exactly what went wrong and what would have prevented it.
The distribution that matters most isn't your blog traffic. It's dark social — security-specific Slack communities, ISAC working groups, Reddit threads, and private LinkedIn networks where CISOs actually share resources. Get your content into those channels and you build credibility at scale before the first outbound touch.
5. Account-Based Marketing (ABM) for Enterprise Cybersecurity
ABM is a natural fit for cybersecurity lead generation because the TAM for most vendors isn't massive — but the deal values are. Spreading outreach thin across a broad list makes less sense than going deep on the accounts that are genuinely worth winning.
The ABM approach for cybersecurity starts with a tightly defined target account list — built on ICP signals like environment type, tech stack, compliance drivers, company size, and industry risk profile. From there, you map outreach across multiple stakeholders simultaneously: CISO, SOC leadership, IT infrastructure lead, and GRC. Each receives messaging relevant to their specific pain and role in the buying committee.
This multi-threading approach does two things. It reduces the risk of a single champion going dark. And it creates internal alignment within the target account that accelerates deal velocity once a conversation opens.
6. Cold Email Outreach with Security-Specific Messaging

Cold email still works in cybersecurity — but only when it's done with precision and credibility. The bar for what "good" looks like is higher here than in almost any other B2B vertical.
What kills cybersecurity cold email immediately:
- Buzzwords like "next-gen," "cutting-edge," or "best-in-class"
- Over-claims about breach prevention or 100% protection guarantees
- Generic openers that could apply to any company in any industry
- Demo-first CTAs that ask for time before establishing any credibility
What actually works is scoped problem framing — referencing a specific risk relevant to their industry, a recent regulatory change, or a known attack pattern targeting their tech stack. Pair that with a low-friction CTA (a quick validation question, not a full demo request) and a clean compliance-safe sending setup that doesn't itself look suspicious to security-trained buyers.
One more thing: GDPR and CAN-SPAM compliance aren't optional in this vertical. Cybersecurity buyers notice, and non-compliant outreach actively damages your brand.
7. Offer Free Compliance or Security Assessments

Free assessments outperform standard lead magnets in cybersecurity because they attract buyers who are already in an evaluation mindset — not just casual researchers. A buyer who requests a CMMC readiness assessment is signaling active intent and timeline in a way that an eBook download never does.
The four highest-converting assessment formats for generating leads for cybersecurity startups and established vendors alike in 2026:
- CMMC Level 2 readiness gap analysis for defense contractors and supply chain.
- Ransomware exposure assessment tied to specific industry attack patterns.
- Cloud security posture review for companies in active cloud migration.
- Zero-trust maturity assessment for enterprise IT transformation programs.
The positioning that converts is specificity. "Free cloud security assessment" is weak. "We'll map your cloud posture against NIST CSF 2.0 and identify the top 3 gaps attackers exploit in your industry" is a different conversation entirely.
Assessments also shorten the sales cycle dramatically by doing pre-qualification before the first call. A buyer who completed your assessment already trusts you and arrives at the meeting with context established.
8. Track CISO Job Changes as a Pipeline Signal
New CISOs are among the most reliably high-converting prospects in the entire cybersecurity lead generation universe. They arrive with a mandate to evaluate existing tools, a budget allocation tied to their agenda, and urgency to make visible progress quickly.
There's also a double opportunity built in. The departing CISO is a champion arriving at a new company — a warm introduction opportunity at a net-new account. The incoming CISO at the original company is a fresh prospect with a clean slate and an evaluation cycle opening.
How to monitor this signal without being intrusive:
- LinkedIn Sales Navigator Champions feature tracks when your contacts change roles.
- Bombora intent feeds surface new leadership combined with technology evaluation signals.
- Google Alerts on "[Company Name] CISO" catch press announcements and LinkedIn posts.
Personalize outreach around the transition: acknowledge the new role, reference a relevant challenge their industry is currently facing, and position your solution as something the best teams in that space are already using.
Keep it human. Don't lead with the fact that you've been tracking their career.
9. Leverage Industry Events and Community Presence

In cybersecurity, peer trust carries more weight than vendor outreach. CISOs reference recommendations from their networks before any sales conversation shapes their thinking. Events and communities are where those networks live.
Key events to build pipeline presence around:
- RSA Conference — the largest gathering of enterprise security decision-makers globally
- Black Hat — technical credibility builder with practitioner-level security leaders
- SC World Awards and regional cybersecurity summits — smaller, higher-trust peer environments
- ISAC working groups — sector-specific information sharing communities where vendors who show up consistently build real credibility
The play isn't a booth and a badge scan. It's pre-event outreach to target accounts (referencing the event as context), genuine conversations at the event, and a structured post-event follow-up sequence within 72 hours while the interaction is still fresh.
Community presence works the same way. Engaging in security-specific Slack groups, contributing to Gartner Peer Insights, and showing up in the spaces where security leaders actually ask questions builds long-term pipeline that outbound alone can't replicate.
10. Speed-to-Lead: Respond to Inbound in Under 5 Minutes
Most cybersecurity vendors invest heavily in generating inbound interest — and then lose it by being slow. The average B2B response time is 42 hours. Yet contacting a lead within the first 5 minutes makes you 21x more likely to turn them into a qualified sales opportunity compared to waiting 30 minutes.
In cybersecurity, this gap is especially costly. Buyers evaluate multiple vendors simultaneously, and the first credible response often controls the entire evaluation. Being second by 24 hours doesn't mean being behind — it means being essentially invisible.
Research from the Lead Response Management Study and Harvard Business Review confirms that contacting leads within five minutes yields 21x higher qualification rates than waiting just 30 minutes.
How to build a fast inbound response system that actually works at scale:
- CRM automation that triggers instant lead routing to the right rep or SDR queue the moment a form submits.
- SDR alert workflows via Slack or SMS so no lead sits in a queue waiting to be noticed.
- AI-assisted first-touch sequences that acknowledge immediately while a rep warms up for a real conversation.
Speed isn't just a metrics play. In cybersecurity, a fast, credible response is itself a trust signal. A vendor who responds within minutes demonstrates organizational competence before the first meeting.
Common Cybersecurity Lead Generation Mistakes to Avoid
Most cybersecurity lead generation programs don't fail because of a single bad decision. They fail because of a combination of avoidable mistakes that compound over time.
❌ Running generic B2B playbooks without cybersecurity-specific positioning.
Security buyers can tell immediately when a sequence was built for a generic B2B audience. The language is wrong, the pain points are vague, and the credibility signals are missing.
❌ Targeting by job title alone without intent or timing signals.
A CISO at a 5,000-person enterprise with no active initiative is not the same prospect as a CISO whose company just experienced a breach. Same title, completely different buying situation.
❌ Over-claiming in messaging.
Security buyers scrutinize every vendor statement professionally. Claims like "prevent 100% of breaches" or "industry-leading protection" immediately signal that you don't understand how security actually works.
❌ Relying on a single outreach channel instead of multi-threading.
With 6–10 stakeholders involved in a typical cybersecurity purchase, a single-channel, single-contact approach misses most of the decision-making entirely.
❌ Treating all inbound leads the same regardless of buying stage.
A CISO requesting a compliance assessment is in a completely different funnel stage than someone who downloaded a threat report. Routing them to the same sequence wastes your highest-intent leads.
How Cleverly Helps Cybersecurity Companies Generate Qualified B2B Leads

Most outbound programs fail cybersecurity vendors not because of lack of effort, but because the targeting is too broad, the messaging is too generic, and there's no system for consistent iteration.
Cleverly specializes in outbound-led B2B lead generation for companies that need precision, not volume. For cybersecurity clients, that starts with building ICP-matched target lists of verified decision-makers — CISOs, IT Directors, VP of Security, and GRC leads — using multi-source data enrichment that reduces wasted touches on unqualified or unready accounts.
From there, our LinkedIn lead gen services are built specifically around trust-building messaging sequences — not generic sales scripts. We research your ICP, identify the right pain points and compliance triggers, and write copy that speaks the language of security buyers from the first message.
Our cold email campaigns follow the same principle: compliance-safe, credibility-first outreach that frames your solution around a specific risk or deadline your buyer already cares about.
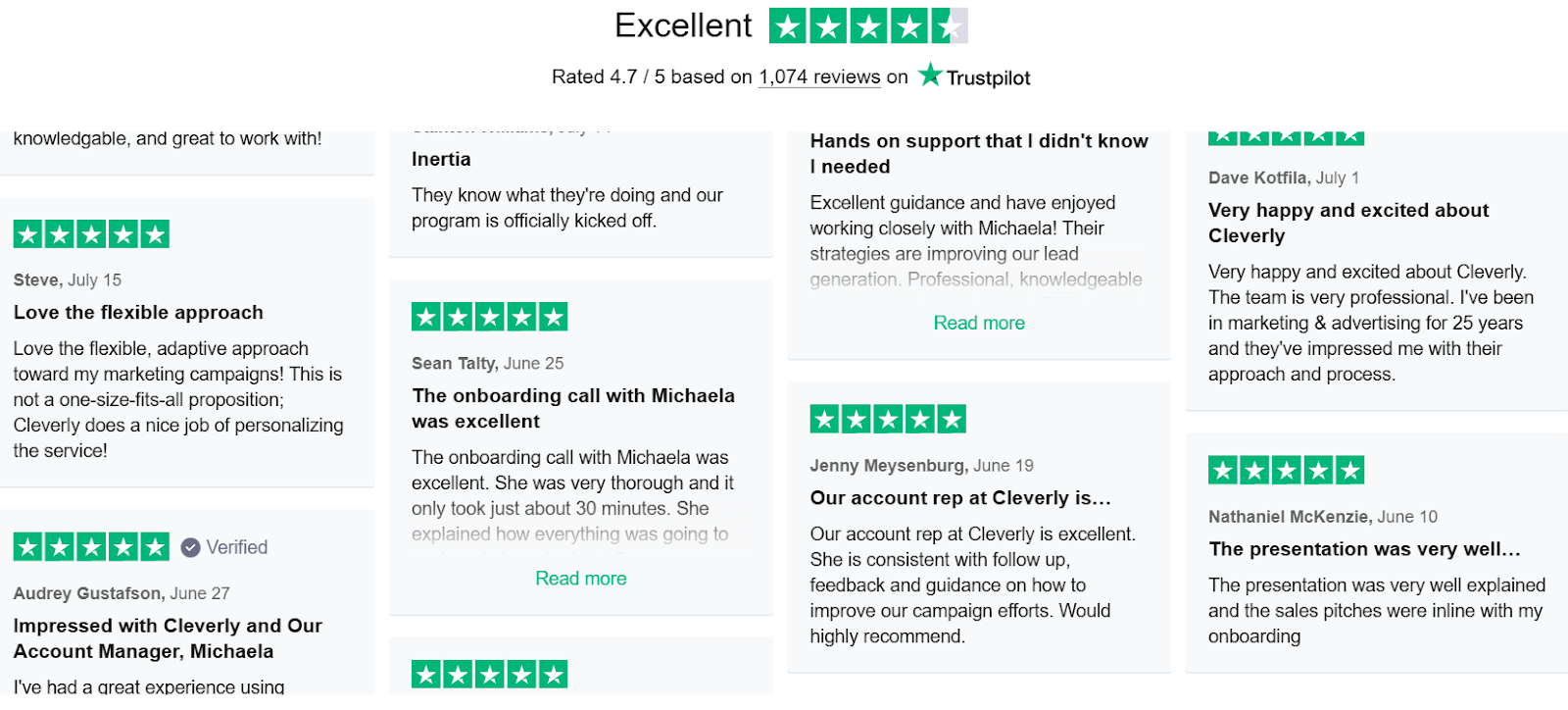
The result is qualified meetings with the right stakeholders — not just contacts and clicks. We've helped 10,000+ B2B companies generate $312M in pipeline, and our model is built on outcomes: month-to-month pricing, no long-term contracts, and a pay-per-performance cold email option so you're only paying for meetings that actually happen.
Want to reach the right cybersecurity decision-makers without burning your brand on bad outreach?
🔥 Book a strategy call with Cleverly.
Conclusion
Cybersecurity lead generation isn't a volume game. It's a precision game. The buyers you're trying to reach are the same professionals who defend organizations against social engineering, fake vendor outreach, and low-credibility pitches every single day.
The 10 strategies in this guide are built around how security buyers actually research, evaluate, and make decisions. Start with intent signals and ICP clarity before scaling any outbound channel. Layer in compliance triggers, thought leadership, and ABM where the deal sizes justify it. And make sure your inbound response system is fast enough to capitalize on the interest you generate.
The companies winning cybersecurity pipeline in 2026 aren't the ones sending the most emails. They're the ones showing up with the most relevance, at exactly the right moment.
Frequently Asked Questions